
Are Fingerprint Scanners Secure?
Biometric Fingerprint readers are generally considered to be one of the most reliable forms of biometric authentication, because they are based on unique physical characteristics that are difficult to duplicate but are fingerprint scanners really secure? Effectively, with biometrics,the authentication credential is a unique biological characteristic which can be used to identify and verify a person’s identity. Apart from fingerprints, we see this in facial recognition scans, DNA tests, and less frequently in palm prints, iris and retina recognition.
While difficult, it’s not impossible to fool fingerprint scanners in some cases, because, like any security measure, they aren’t foolproof if the attackers are skilled and determined enough.
Here are a few ways a fingerprint scanner could be fooled:
Fake fingerprints:
It is possible to create fake fingerprints using materials like silicone, gelatin and other materials. Fake prints can sometimes fool fingerprint scanners that are not designed to detect such attempts.
Latent fingerprints:
In some cases, an attacker can obtain a person’s fingerprint from a surface they’ve touched, such as a glass or a doorknob, and then use that to create a fake fingerprint.
Low-quality sensors:
Some fingerprint scanners are not very sensitive or may have low-quality sensors that can be tricked by fake or altered fingerprints.
Malware or hacking:
Attackers may use malware or other hacking techniques to bypass fingerprint scanner security measures or to intercept unencrypted data between the fingerprint scanner and the processing software. Sometimes these employ a so called ‘masterprint’, these are a manufactured print which would include all of the standard features on anyone’s fingerprint.
Is the risk really that high?
It’s important to note that these methods of fooling fingerprint scanners require significant effort and resources. In most cases, the use of a fake or altered fingerprint would require a high degree of skill and knowledge, making it unlikely to be a major security concern for most people.
Additionally, newer fingerprint scanners often have more advanced security features that make them more difficult to trick. A ‘masterprint’ would only work on a sub-par fingerprint scanner that doesn’t look at the finer details when it’s looking to compare a biometric template against the one held in its database.
In terms of security, modern fingerprint scanners are also designed to be resistant to the above types of attacks, including fake fingerprints, latent prints, and other attempts to trick the system. They use advanced algorithms and sensors that can detect when a fingerprint is not genuine.
Drawbacks:
When Apple introduced Touch ID in 2013, the technology was compromised within just 2 days and since then dental mold and play-dough has successfully bypassed the system. This may ring alarm bells, but questions should be asked as to how advanced/ high quality the scanner was and how high the matching threshold was.
There is probably more of a risk that the back up PIN number could be hacked, or obtained through ‘shoulder surfing’ (where the attackers merely look over the target’s shoulder and sees them input their pin), than hackers going to the trouble of obtaining your fingerprint to open your phone.

There is the issue that once biometric data such as a fingerprint is stolen, it’s stolen forever. Unlike a password, it can’t be changed. It’s even more of a reason that only high-quality fingerprint scanners should be used, because they don’t actually store a picture of your fingerprint. After the enrolment process there is only an encrypted biometric template which can’t be backwards engineered to a picture of your fingerprint.
Stolen biometric data could theoretically be used to identify users without their knowledge, especially if users are unaware of how their data is stored, collected and used. Voice authentication is a technology gaining traction, but the UK’s HMRC received a fine in 2019 for breaching GDPR by verifying users using their voices without obtaining explicit consent (read the full story here).
Interestingly, HMRC will continue to use the technology as they believe it to be secure and promotes a good user experience, the issue was that the collection and usage had not been clearly explained to members of the public and they weren’t given the option to opt out, thereby contravening GDPR.
Use a High-Quality Scanner
It’s vital therefore that if considering using fingerprint scanners, you choose the manufacturer and installer wisely. Cheap readers from auction sites aren’t likely to have the same built in safeguards that high-quality scanners will have when they come from a recognised manufacturer, who adheres to strict installation protocols and GDPR policies.
Choosing your Installer
Your installer should be registered with a national body such as NSI or SSAIB in the UK, and must be PSA accredited in Ireland. This means they are audited to ensure that they have physical and digital security measures in place, vetting processes for their team and that they follow strict procedures in the way they conduct installations.
Conclusion
For the majority of applications good quality, certified fingerprint scanners and software are sufficient to both deter and stop criminals. For high-security environments they can also be integrated with other security measures, such as passwords or two-factor authentication, to provide an additional layer of protection.
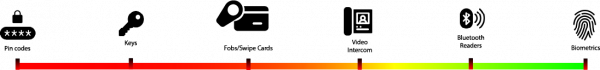
Fingerprint scanners check who someone is, rather than what they know (a pin code) or credentials they carry (card/ fob), so in our scale of security, they come right at the top.
The first fingerprint scanners were used by the FBI in 1969 – they’ve come a long way since then and been absorbed into mainstream applications such as smartphone and commercial access control.
The accountability of knowing that the individual is definitely who you expect them to be, means that you can also utilise the data for clocking in, to prove working time directive compliance, and to stamp out tardiness. Fingerprint scanners are not just about letting someone in a building any more.
Get in touch if you’d like more information
You can call us on 03335677799 or 016833368 or email us: [email protected]




